Discretionary and Non-Discretionary Access Control Policies by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu

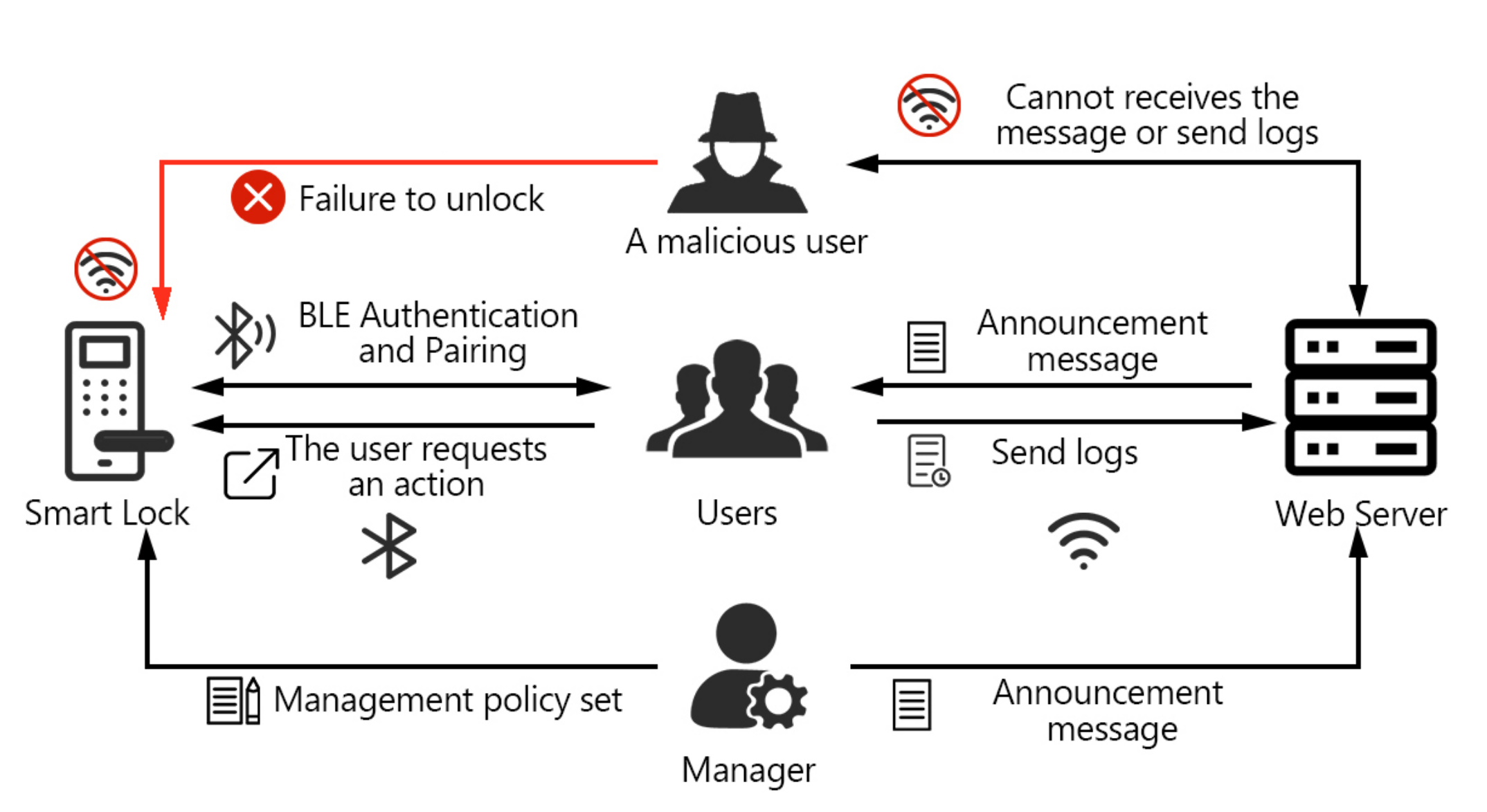
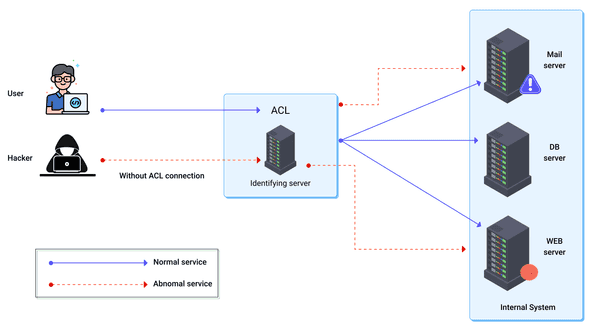
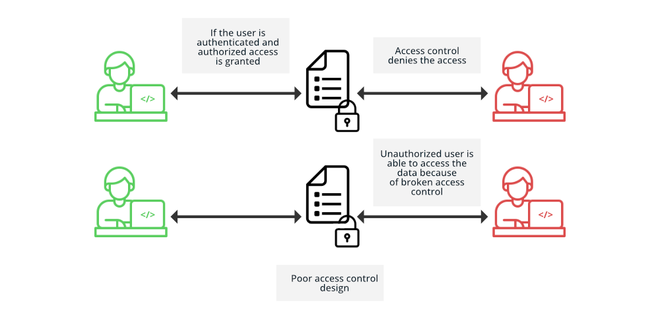
Figure 1 from A decentralized access control mechanism using authorization certificate for distributed file systems | Semantic Scholar

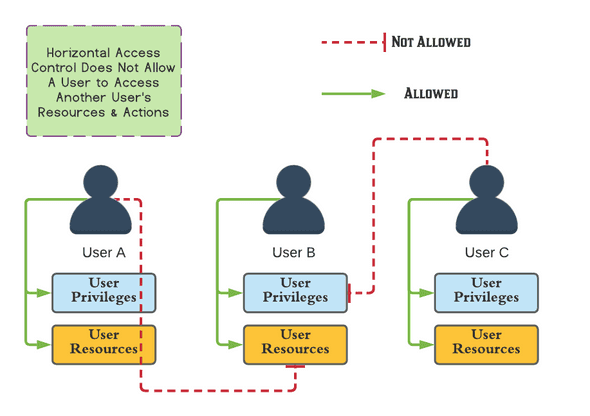
Symmetry | Free Full-Text | Permission-Based Separation of Duty in Dynamic Role-Based Access Control Model

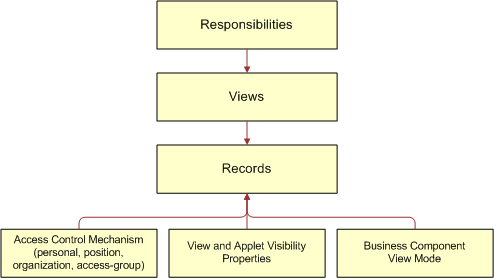
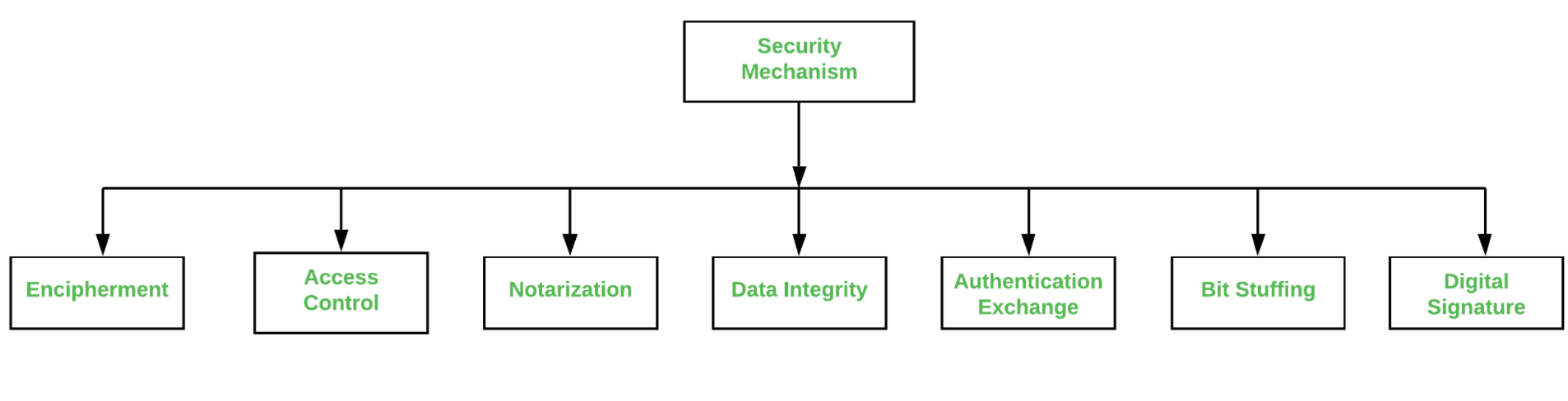
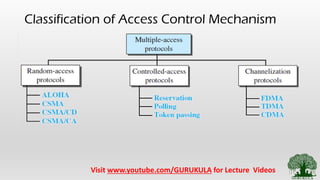
Architecture Of Access Control Mechanism In Run Time Change Management | Download Scientific Diagram